Introduction: Honeypots are invaluable tools for gathering threat intelligence & gaining insights into potential network threats. By mimicking legitimate network components, they attract cybercriminals, diverting them from actual assets & revealing their exploitation techniques.
Honeypot Deployment Strategy:
- Initial Setup: Initially, the honeypot was deployed on a cloud instance to enhance its attractiveness to potential attackers.
- Duration: The honeypot ran for 30 days in one location. The plan is to relocate it every 30 days to observe different Tactics, Techniques, & Procedures (TTPs) based on location.
- Future Expansion: Limited financial resources currently restrict the deployment to multiple continents, but this is a desired future state for a more comprehensive threat landscape understanding.
Key Focus Areas:
- Attacker Services & Safe Havens: Identify the services & locations used by attackers.
- Bot & Scan Activities: Determine the extent of bot & scan activities.
- Unusual Behaviors & Tactics: Detect unique attacker behaviors not typically recorded in common databases.
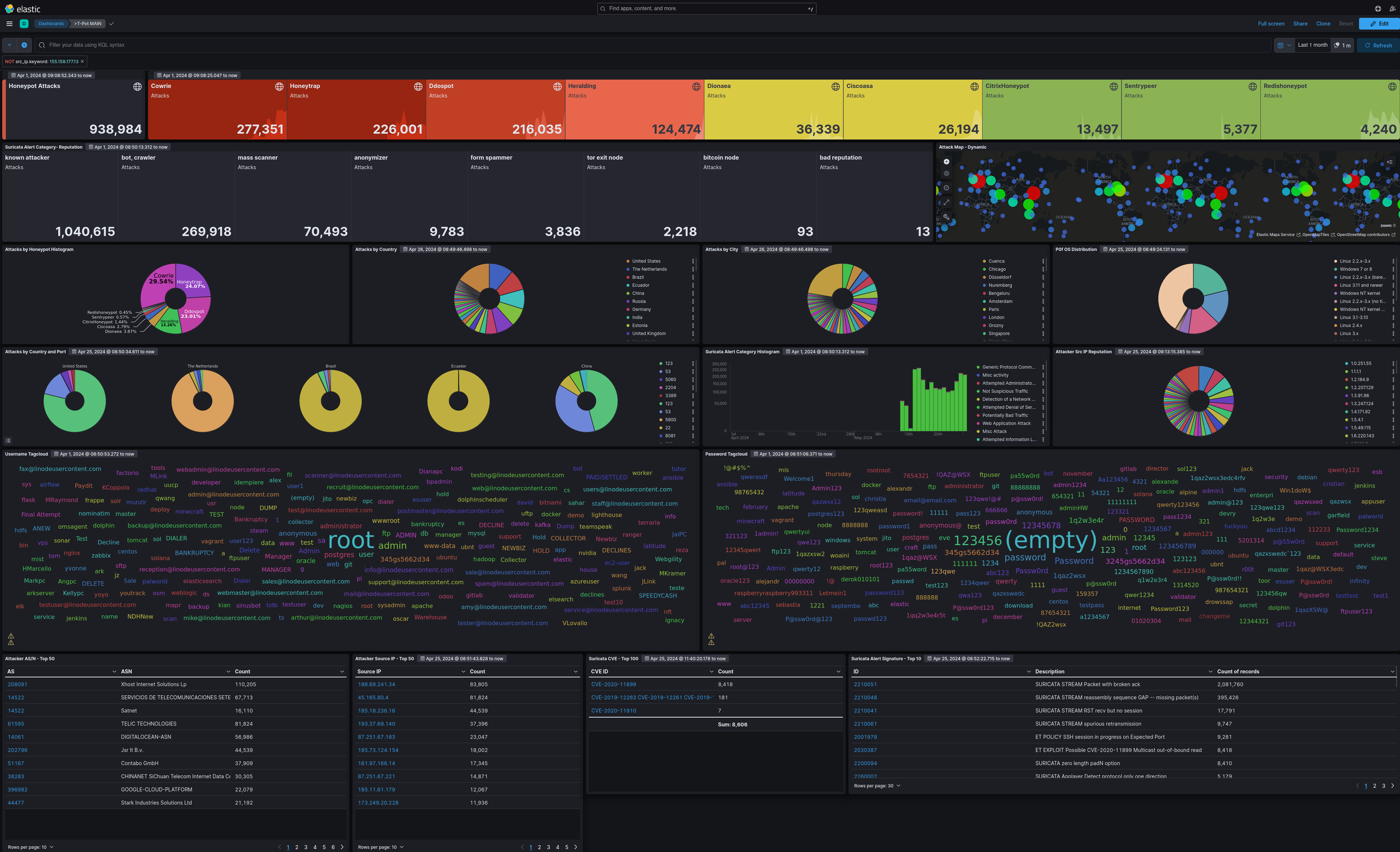
Total number of attacks recorded over a 30 day period.
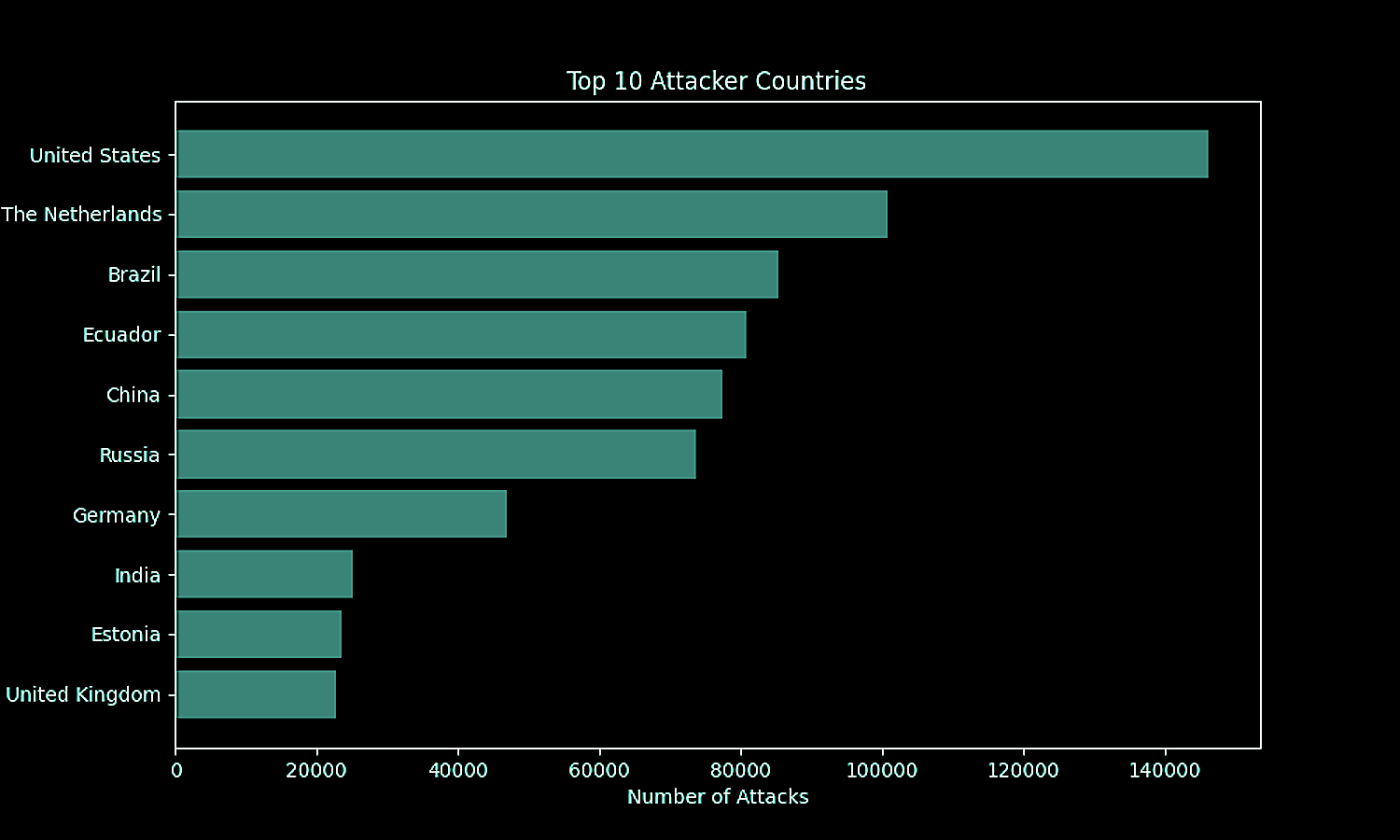
1. Top 10 Attacker Locations
Countries
1. United States: 146,124
2. The Netherlands: 100,672
3. Brazil: 85,401
4. Ecuador: 80,759
5. China: 77,505
6. Russia: 73,564
7. Germany: 46,954
8. India: 25,057
9. Estonia: 23,469
10. United Kingdom: 22,752
Cities
1. Cuenca: 80,708
2. Chicago: 19,528
3. Düsseldorf: 16,754
4. Nuremberg: 14,640
5. Bengaluru: 14,160
6. Amsterdam: 13,585
7. Paris: 12,491
8. London: 12,081
9. Grozny: 11,766
10. Singapore: 11,203
2. Attacks by Reputation, TTP
Known Attackers – 1,031,819
- Tactic: Initial Access
- Techniques: Use of compromised credentials, exploitation of public-facing applications
- Procedure: Attackers using known attacker infrastructure (IPs, domains) to gain initial access to systems.
Bots, Crawlers – 269,651
- Tactic: Discovery
- Techniques: Automated scanning, web crawling
- Procedure: Bots & crawlers scanning for vulnerabilities, open ports, & exploitable services.
Mass Scanners –69,871
- Tactic: Reconnaissance
- Techniques: Network scanning, port scanning
- Procedure: Attackers using tools to scan large ranges of IPs to find potential targets.
Anonymizers – 9,783
- Tactic: Defense Evasion
- Techniques: Use of anonymizing services (VPNs, Tor)
- Procedure: Attackers masking their origin by routing traffic through anonymizers to avoid detection.
Form Spammers – 3,836
- Tactic: Impact
- Techniques: Spam
- Procedure: Automated tools submitting forms to spread spam or perform phishing attacks.
Tor Exit Nodes – 2,218
- Tactic: Defense Evasion
- Techniques: Use of Tor network
- Procedure: Attackers using Tor exit nodes to anonymize their activity & evade detection.
Bitcoin Nodes – 93
- Tactic: Command & Control
- Techniques: Peer-to-peer communication
- Procedure: Using Bitcoin nodes for command & control infrastructure, potentially for malware operations.
Bad Reputations – 13
- Tactic: Initial Access
- Techniques: Brute Force, Exploitation of Vulnerabilities
- Procedure: Using IPs known for malicious activities to attempt brute force or exploit known vulnerabilities.
SURICATA STREAM Packet with broken ack – 1,342,334
ET EXPLOIT Possible CVE-2020-11899 Multicast out-of-bound read – 6,552
SURICATA HTTP missing Host header – 744
ET DOS Likely NTP DDoS In Progress MON_LIST Response to Non-Ephemeral Port IMPL 0x03 – 588
3. Potential Script Execution Attempts
- ET EXPLOIT Possible VXWORKS Urgent11 RCE Attempt – Urgent Flag – Number of Attacks: 71
- ET EXPLOIT Possible VXWORKS Urgent11 RCE Attempt – Illegal Urgent Flag – Number of Attacks: 71
- ET EXPLOIT Linksys E-Series Device RCE Attempt Outbound – Number of Attacks: 53
- ET EXPLOIT Possible CVE-2020-11899 Multicast out-of-bound read – Number of Attacks: 6,552
- ET EXPLOIT Possible CVE-2020-11910 anomalous ICMPv4 type 3,code 4 Path MTU Discovery – Number of Attacks: 4
- ET INFO Cisco Smart Install Protocol Observed – Number of Attacks: 38
Insights
- The most significant script execution attempts involve the exploitation of specific vulnerabilities like VXWORKS Urgent11 & CVE-2020-11899.
- There is a notable number of attempts to exploit Linksys devices & use the Cisco Smart Install protocol, which may indicate ongoing efforts to compromise network equipment.
- These attempts are distributed across different attack signatures, showing a variety of methods being used to achieve remote code execution.
By monitoring & analyzing these specific alert signatures, security teams can gain insights into the attacker’s methods & take appropriate actions to mitigate these threats.
4. Potential (C2) Contact Attempts
- ET POLICY SSH session in progress on Expected Port – Number of Attacks: 5,845
- ET POLICY SSH session in progress on Unusual Port – Number of Attacks: 1,963
- ET INFO Potentially unsafe SMBv1 protocol in use – Number of Attacks: 1,097
- ET SCAN Zmap User-Agent (Inbound) – Number of Attacks: 670
- ET SCAN Mirai Variant User-Agent (Inbound) – Number of Attacks: 17
- ET SCAN RDP Connection Attempt from Nmap – Number of Attacks: 5
- ET INFO Cisco Smart Install Protocol Observed – Number of Attacks: 38
Insights
Script Execution Attempts:
- There are multiple attempts to exploit vulnerabilities that could lead to remote code execution (RCE). These include known vulnerabilities like VXWORKS Urgent11 & others that involve exploiting specific protocols or devices.
C2 Contact Attempts:
- There are numerous SSH sessions in progress, which could indicate attempts to establish persistent access or contact C2 servers. The use of unusual ports for SSH sessions further suggests possible C2 activity.
- Other protocols & services such as SMBv1 & specific user-agent strings (e.g., Mirai Variant) indicate attempts to communicate with external servers potentially associated with C2 infrastructure.
5. Top 15 ASNs
An Autonomous System Number (ASN) is a unique identifier assigned to an autonomous system (AS) on the internet. An autonomous system is a collection of IP networks & routers under the control of a single organization that presents a common routing policy to the internet. ASNs are crucial for facilitating routing on the internet, as they allow different networks to communicate with each other.
The way it’s supposed to work is if you identity that an attacker is launching from a specific service provider, you let that service provider know & they do something about it.
That’s not the way it works. Since singing up for these services is completely automated, even with the best of intentions a service can take hours, if not days to confirm & do something about it, which is enough time to completely pwn someone & be on their way.
Check out #9, ASN: 44477-Stark Industries Solutions. Brian Krebs (Krebs On Security) did an extensive write up on Stark Industries, known as a *bullet proof service provider. I highly recommend reading it get an understand of how easy it is for attackers to find safe haven from which to launch attacks.
* They ignore reports & complaints about their services being used to conduct cyber attacks providing a safe haven to attackers.
1. ASN: 208091
Company: Xhost Internet Solutions LP
Country: United Kingdom
Number of Attacks: 110,148
2. ASN: 14522
Company: SERVICIOS DE TELECOMUNICACIONES SETEL S.A. XTRIM EC
Country: Ecuador
Number of Attacks: 64,660
3. ASN: 61595
Company: TELIC TECHNOLOGIES
Country: South Africa
Number of Attacks: 80,309
4. ASN: 14061
Company: DIGITALOCEAN-ASN
Country: United States
Number of Attacks: 56,699
5. ASN: 202796
Company: Jsr It B.V.
Country: Netherlands
Number of Attacks: 44,539
6. ASN: 51167
Company: Contabo GmbH
Country: Germany
Number of Attacks: 37,267
7. ASN: 38283
Company: CHINANET SiChuan Telecom Internet Data Center
Country: China
Number of Attacks: 30,303
8. ASN: 396982
Company: GOOGLE-CLOUD-PLATFORM
Country: United States
Number of Attacks: 22,029
9. ASN: 44477
Company: Stark Industries Solutions Ltd
Country: United Kingdom
Number of Attacks: 20,538
10. ASN: 137951
Company: ASLINE LIMITED
Country: Hong Kong
Number of Attacks: 20,276
11. ASN: 132203
Company: Tencent Building, Kejizhongyi Avenue
Country: China
Number of Attacks: 16,743
12. ASN: 57523
Company: Chang Way Technologies Co. Limited
Country: Hong Kong
Number of Attacks: 15,532
13. ASN: 267827
Company: PERALTA LEANDRO NAHUEL
Country: Argentina
Number of Attacks: 13,577
14. ASN: 4134
Company: Chinanet
Country: China
Number of Attacks: 13,525
15. ASN: 399486
Company: VIRTUO
Country: United States
Number of Attacks: 12,316
6. High Volume Attackers
IP Address: 186.69.241.34
- Number of Attacks: 80,752
Type: SSH on unusual port, High volume attacks - Service Provider: SERVICIOS DE TELECOMUNICACIONES SETEL S.A. XTRIM EC (ASN: 14522)
- Country: Ecuador
- Number of Attacks: 80,752
IP Address: 45.165.80.4
- Number of Attacks: 80,309
- Type: SSH on unusual port, High volume attacks
- Service Provider: SERVICIOS DE TELECOMUNICACIONES SETEL S.A. XTRIM EC (ASN: 14522)
- Country: Ecuador
IP Address: 185.18.236.16
- Number of Attacks: 44,539
- Type: SSH on unusual port, High volume attacks
- Service Provider: Leaseweb Deutschland GmbH (ASN: 28753)
- Country: Germany
IP Address: 193.37.69.140
- Number of Attacks: 37,396
- Type: SSH on unusual port, High volume attacks
- Service Provider: Transip B.V. (ASN: 20857)
- Country: Netherlands
IP Address: 87.251.67.183
- Number of Attacks: 23,047
- Type: SSH on unusual port, High volume attacks
- Service Provider: FIORD-AS (ASN: 28917)
- Country: Russia
IP Address: 185.73.124.154
- Number of Attacks: 18,002
- Type: SSH on unusual port, High volume attacks
- Service Provider: WorldStream B.V. (ASN: 49981)
- Country: Netherlands
IP Address: 161.97.166.14
- Number of Attacks: 16,704
- Type: SSH on unusual port, High volume attacks
- Service Provider: Hetzner Online GmbH (ASN: 24940)
- Country: Germany
IP Address: 87.251.67.221
- Number of Attacks: 14,871
- Type: SSH on unusual port, High volume attacks
- Service Provider: FIORD-AS (ASN: 28917)
- Country: Russia
IP Address: 185.11.61.179
- Number of Attacks: 12,067
- Type: SSH on unusual port, High volume attacks
- Service Provider: OVH SAS (ASN: 16276)
- Country: France
IP Address: 173.249.20.228
- Number of Attacks: 11,936
- Type: SSH on unusual port, High volume attacks
- Service Provider: Hetzner Online GmbH (ASN: 24940)
- Country: Germany
Insights
Ecuador:
- The top two IPs from Ecuador belong to the same service provider & ASN, indicating coordinated activities or a shared infrastructure used for potential C2 operations.
Germany & Netherlands:
- Multiple IPs from these countries indicate the use of European hosting services for potential C2 activities. Hetzner Online GmbH & Leaseweb Deutschland GmbH are notable service providers.
Russia:
- IPs from Russia linked to the FIORD-AS ASN show repeated & high-volume attacks, suggesting significant C2 potential.
France:
- The IP from France (OVH SAS) is also a known hosting provider used in various cyber activities.
Actionable Steps
Monitor & Block:
- Continuously monitor these IP addresses for C2-related behaviors & consider blocking them at the firewall or IDS/IPS level to prevent potential malicious activities.
Further Investigation:
- Conduct a deeper investigation into the activities originating from these IPs to identify specific C2 commands or payloads.
Update Threat Intelligence Feeds:
- Share these findings with threat intelligence platforms to update the cybersecurity community about potential C2 IP addresses.
7. Identified Downloads & Malware
eyshcjdmzg
- File: ea40ecec0b30982fbb1662e67f97f0e9d6f43d2d587f2f588525fae683abea73
- Attacker IP: 218.92.0.60 › China
- Number of Attacks: 10
sshd
- File: 326a7c1bece04c1e4efd6db106d3f09687c3a82398064568985372374fb12cdf
- Attacker IP: 117.66.249.166 › China
- Number of Attacks: 1
sshd
- File: 6e08a9b19df98e36da4409a8ae5990bde3ed6dc583fbea9f112cbc55421aec59
- Attacker IP: 223.210.14.226 › China
- Number of Attacks: 1
sshd
- File: 7cf3855397bd54a838d1445f2a6527169e428021d1e77537dda1ad6ca9ffb4ae
- Attacker IP: 168.90.18.141 › Brazil
- Number of Attacks: 1
sshd
- File: 94f2e4d8d4436874785cd14e6e6d403507b8750852f7f2040352069a75da4c00
- Attacker IP: 167.114.114.148 › Canada
- Number of Attacks: 1
sshd
- File: 9e6563cc3e801577c11b4f076cec3dd1c268dce1e1b117ea6a8cd99be6db3ef0
- Attacker IP: 117.50.197.190 › China
- Number of Attacks: 1
sshd
- File: ab31ea17ea415efd30a19fdb7a68b92146692b76584007cbbb94f55b9761b8dc
- Attacker IP: 125.124.179.148 › China
- Number of Attacks: 1
sshd
- File: e41ff2d7a604a3ee1c1d99502b390adf9cf7119f1b6b7902ea26b88c148cb451
- Attacker IP: 36.158.206.226 › China
- Number of Attacks: 1
sshd
- File: f4d2b5812f522b66a4a6ea5b979cae2b73486618708158e5ef61c469b2306f24
- Attacker IP: 123.131.17.131 › China
- Number of Attacks: 1
redtail.arm7
- File: 6f922abf3efc96d286a432e6bfdef73a44a6f4257bc9f36f460a57959180e49a
- Attacker IP: 78.153.140.51 › United Kingdom
- Number of Attacks: 3
redtail.arm8
- File: a728692cf481ed612a35421967a9a499bf1b74f5771059002dfa42c413dda6c7
- Attacker IP: 78.153.140.51 › United Kingdom
- Number of Attacks: 3
redtail.i686
- File: e89b79c039776ff64e4979a80fa95c020161a98f8cb434fbfd09f409ba73bd9e
- Attacker IP: 78.153.140.51 › United Kingdom
- Number of Attacks: 3
Insights:
High Frequency IPs:
- The IP address
218.92.0.60from China has the highest number of download attempts (10 times), indicating persistent efforts to download a file namedeyshcjdmzg.
- The IP address
Malware Indicators:
- Files with the name
sshdare commonly used in SSH-based attacks & may indicate attempts to deploy backdoors or other malicious software. - The filenames
redtail.arm7,redtail.arm8, &redtail.i686suggest downloads targeting different architectures, possibly indicating attempts to deploy multi-platform malware.
- Files with the name
Countries of Origin:
- Multiple download attempts originate from IPs in China, Brazil, Canada, & the United Kingdom, suggesting a diverse range of attack sources.
Actionable Steps:
Investigate Downloads:
- Analyze the downloaded files (e.g.,
eyshcjdmzg,sshd,redtail.*) using a sandbox environment to determine their behavior & potential maliciousness.
- Analyze the downloaded files (e.g.,
Monitor & Block IPs:
- Continuously monitor activities from the identified IP addresses.
- Consider blocking these IP addresses at the firewall or IDS/IPS level to prevent further malicious attempts.
Update Threat Intelligence:
- Share findings about these IPs & downloaded files with threat intelligence platforms to update the cybersecurity community.
Additional Observations: Breach Data
I also recorded 1000’s of attempted usernames & passwords & have found most of the email addresses in HaveIBeenPwned, including what looks like MANY company email addresses. In my opinion, this indicates that attackers are using breach data in brute force attacks. Based on this it is my opinion that IT leaders should set strong boundaries against using company email for non company business.
Conclusion:
The honeypot data reveals critical insights into the behavior & tactics of attackers. By focusing on high-risk ASNs, monitoring identified IPs, & analyzing downloaded files, network security teams can better protect against potential threats.
This is just as mere sliver of the data available. If I were on a specific mission I could focus the data collection to the areas of importance for the organization.

Multi-disciplinary IT support strategist with 15+ years experience empowering entrepreneurs, corporate colleagues and remote teams with the knowledge, skills and technologies to get stuff done. | Sec+ – CySA+ (CSAP) – ITIL – ACSP
Comments are closed.